Description:
This is an issue found when use Clair to scan image vulnerability of RHEL9 image, like "registry.access.redhat.com/ubi9:latest", as there's no CVE data of RHEL9, so Clair report the scan results as passed, this is not correct results, the expected results should be like "not-supported" or "unable to scan", pls review this issue and improve this point.
Clair Version: V4.4.4
{"level":"info","component":"main","version":"v4.4.4","time":"2022-07-13T05:55:24Z","message":"starting"}The following is the list of Clair Dist:
postgres=# select * from dist;
id | name | did | version | version_code_name | version_id | arch |
cpe | pretty_name
----+---------------------------------+--------+-------------------------+-------------------+------------+------+--------------
-------------------------------------+-----------------------------------
1 | Oracle Linux Server | ol | 8 | Oracle Linux 8 | 8 | |
| Oracle Linux Server 8
2 | Red Hat Enterprise Linux Server | rhel | 8 | | 8 | | cpe:2.3:o:red
hat:enterprise_linux:8:*:*:*:*:*:*:* | Red Hat Enterprise Linux Server 8
4 | Ubuntu | ubuntu | 20.04 LTS (Focal Fossa) | focal | 20.04 | |
| Ubuntu 20.04 LTS
5 | SLES | sles | 15 | | 15 | |
| SUSE Linux Enterprise Server 15
6 | Red Hat Enterprise Linux Server | rhel | 7 | | 7 | | cpe:2.3:o:red
hat:enterprise_linux:7:*:*:*:*:*:*:* | Red Hat Enterprise Linux Server 7
7 | Debian GNU/Linux | debian | 10 (buster) | buster | 10 | |
| Debian GNU/Linux 10 (buster)
8 | Amazon Linux | amzn | 2 | | 2 | | cpe:2.3:o:ama
zon:amazon_linux:2:*:*:*:*:*:*:* | Amazon Linux 2
9 | Alpine Linux | alpine | 3.13 | | | |
| Alpine Linux v3.13
(8 rows)
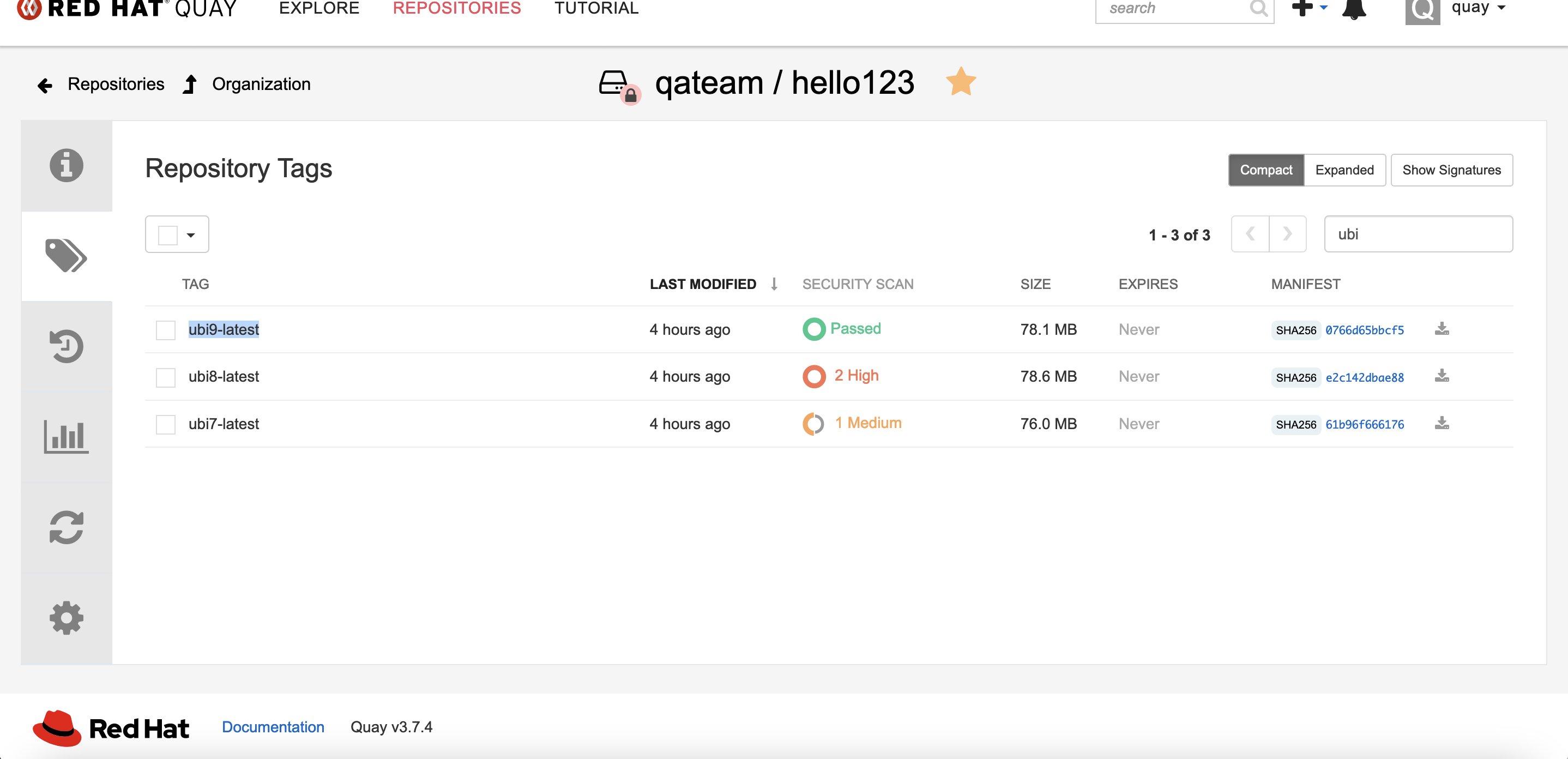
Clair Scan RHEL9 UBI image: