-
Bug
-
Resolution: Obsolete
-
Major
-
None
-
quay-v3.6.1
-
False
-
False
-
-
0
Description:
Register a GitHub application in github.com, generate a pair of valid client id and secret. Then in quay config tool UI, enable 'GitHub Authentication' and choose "GitHub Enterprise", input a bogus github enterprise endpoint and the valid client id and secret generated in github.com, quay config tool treat this setting as valid configuration.
Version-Release number of selected component (if applicable):
$ oc get $(oc get pod -l name=quay-operator-alm-owned -o name -n quay-enterprise) -o jsonpath='{.spec.containers[0].image}' -n quay-enterprise registry.redhat.io/quay/quay-operator-rhel8@sha256:ed4bd0462c25674816db58242bf4631663a22731db58f958b69bd34937e01255
How reproducible:
always
Steps to Reproduce:
1. Follow the below doc Registering a GitHub application to register a gitHub application in github.com, generate a pair of valid client id and secret.
2. Enable the "Enable GitHub Authentication" and choose "GitHub Enterprise"
3 Input a bogus "GitHub Endpoint" and the valid client id and secret generated in github.com
4.Click "Validate Configuration Changes" button to valid the wrong value.
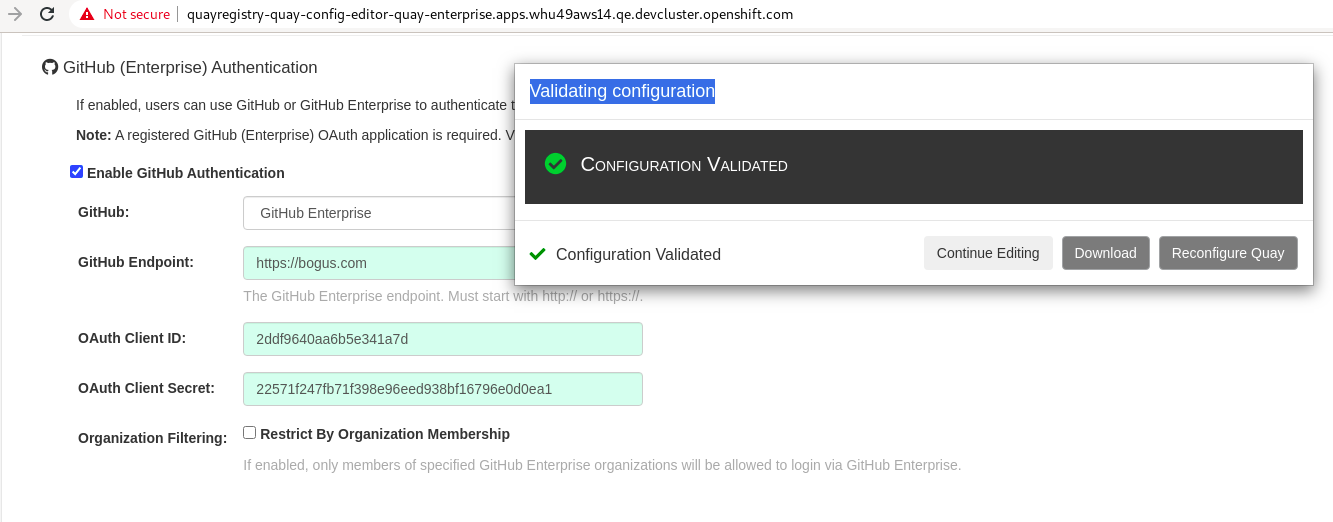
Actual results:
The wrong setting pass config tool validation.
Expected results:
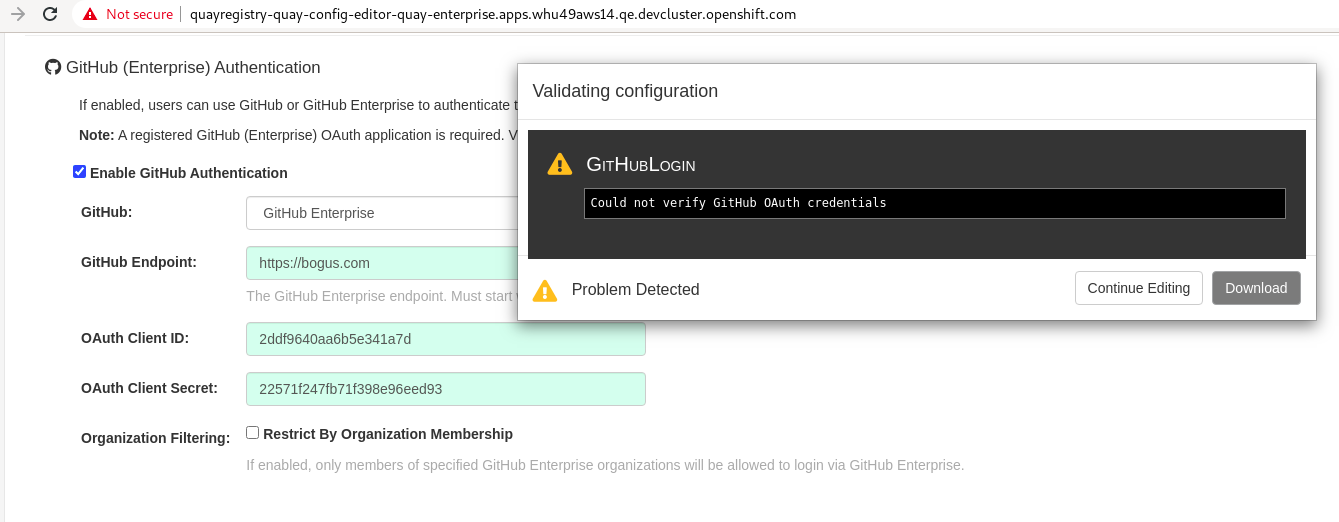
The wrong setting should not pass config tool validation.
Additional info
If input the valid client id and invalid client secret, the validation will be failed as what we expect.
It seems quay config tool confuses the setting between github.com and github enterprise.

