-
Feature
-
Resolution: Unresolved
-
Critical
-
None
-
None
-
Product / Portfolio Work
-
-
-
False
-
-
False
-
None
-
Approved
-
-
-
-
None
-
None
-
None
-
None
Feature Overview
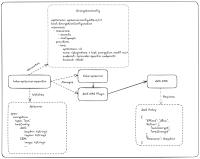
This feature aims to enable customers of OCP to integrate 3rd party KMS solutions for encrypting etcd values at rest in accordance with: https://kubernetes.io/docs/tasks/administer-cluster/kms-provider/
OpenShift Enhancement
https://github.com/openshift/enhancements/pull/1872
Goals
- Adopt KMS v2 Plugin Interface: Implement the feature using the Kubernetes KMS v2 protocol only.
- Automatically deploy, monitor, and manage the lifecycle of the necessary KMS plugin pods to establish communication between the OpenShift API server and the external Key Management Service (KMS).
- Expose User Interface: Extend the APIServer configuration to be the single source of truth for KMS. encryption and connection details.
- Provide similar UX experience for all of self-hosted, HyperShift, SNO scenarios.
- Resilience: Document failure scenarios.
General Prioritization for the Feature
Approved design for detection & actuation for stand-alone OCP clusters.
- Monitor KMS State:
- Provide users with the means to monitor the state of the KMS plugins and the KMS itself.
- Report Status Clearly: Surface KMS plugin status and key rotation progress via Conditions in the APIServer CR’s Status.
- How to detect a problem like an expired/lost key and no contact with the KMS provider?
- How to inform/notify the situation, even at node level, of the situation
- Library-go encryption controller changes
- Tech Preview (Feature gated) enabling Kube-KMS v2 for partners to start working on KMS plugin provider integrations:
- AWS KMS: https://github.com/kubernetes-sigs/aws-encryption-provider
- HashiCorp Vault (HashiCorp currently developing new plugin)
- Optional: Thales: https://github.com/ThalesGroup/k8s-kms-plugin
- is blocked by
-
AUTH-346 Make it possible to remove resources that cannot be accessed due to encryption issues
-
- Closed
-
- is cloned by
-
OCPSTRAT-1638 [GA] Support Kube KMS Integration in OCP (User-Provided)
-
- New
-
-
OCPSTRAT-2598 [DP] Support Kube KMS Integration in OCP (User-Provided)
-
- Closed
-
- is depended on by
-
OCPPLAN-9632 Deliver Supported AWS KMS provider for etcd encryption
-
- New
-
-
OCPPLAN-9633 Deliver Supported Azure KMS provider for etcd encryption
-
- New
-
- is related to
-
AUTH-346 Make it possible to remove resources that cannot be accessed due to encryption issues
-
- Closed
-
-
OCPSTRAT-1625 [Blocked] Validate Hashicorp Vault with Kube KMS for OpenShift Core
-
- Backlog
-
- links to