-
Bug
-
Resolution: Done
-
Critical
-
ACM 2.16.0
Description of problem:
Fleet virtualization tree view relies on ACM search for showing Clusters -> VM namespaces -> VMs. However search will only populate the tree view data if the user has a ClusterRoleBind that includes all namespaces in VM cluster. This causes issues with the end to end fine grained rbac feature when used with the Fleet virtualization UI, because it forces users to ClusterRoleBind acm-vm-extended:view. This goes against the principle of least privilege, and will force customers to give extra permissions just to get the tree view to work.
For example, we expected this to be the minimum privilege for viewing VMs in 1 VM namespace:
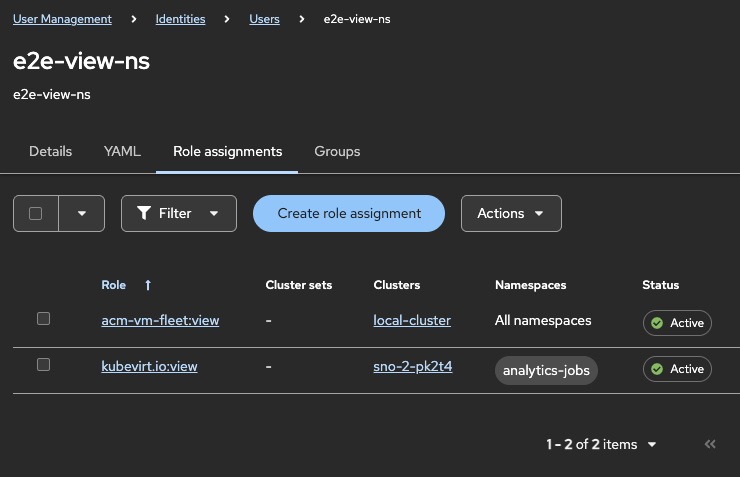
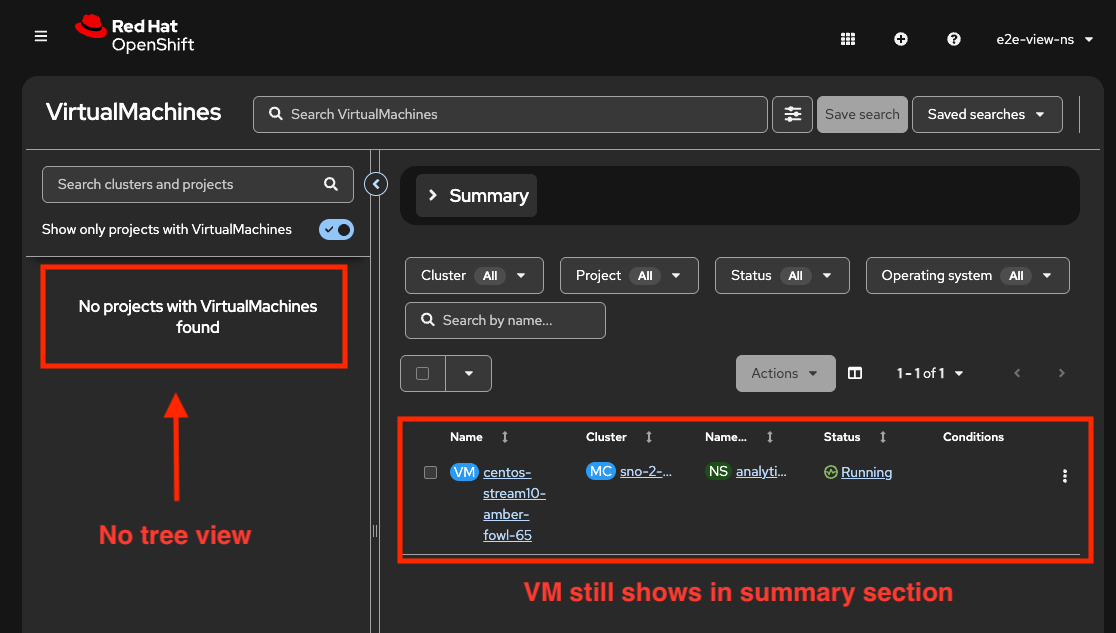
acm-vm-fleet:view is always needed as ClusterRoleBinding on hub. We expected that one could do a RoleBinding to 1 VM namespace with kubevirt.io:view. However this does not allow the tree view to load:
This behavior differs from 2.15. Search would populate namespaces based on kubevirtprojects response. It seems since we changed to the userpermissions api, search does not do this.
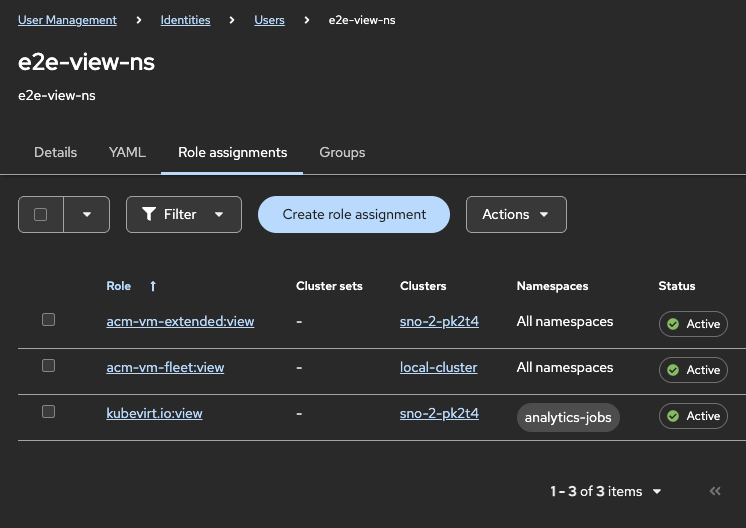
With this current behavior, the least privilege required with the ACM VM roles we currently have is by adding acm-vm-extended:view ClusterRoleBinding on spoke VM cluster:
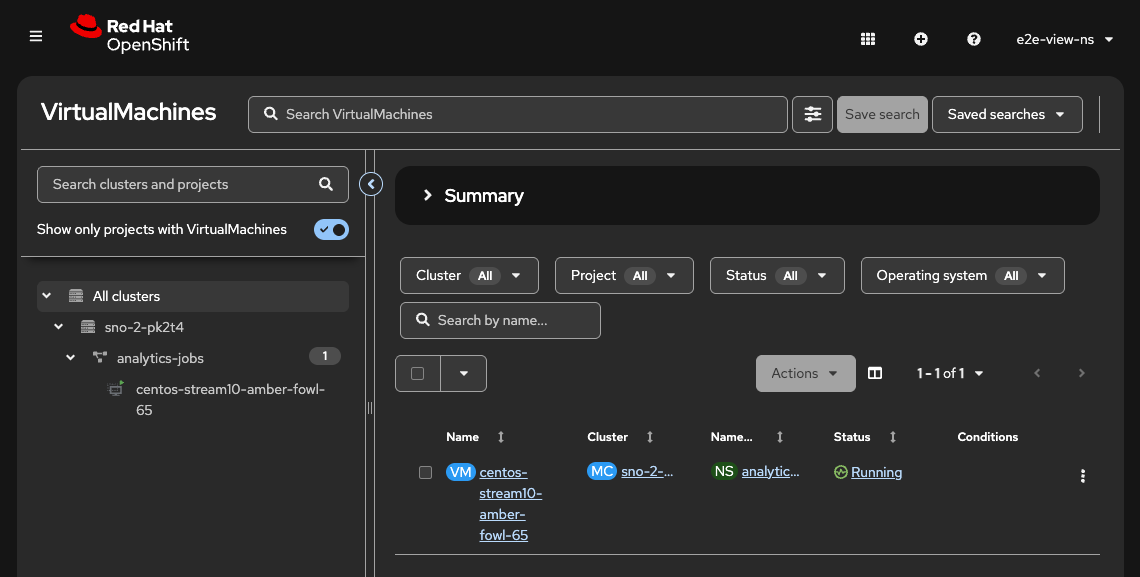
So this role binding combination is working, however it is not ideal for customers who want to give VM admins the least privilege. If a customer only wants to give minimal access to a VM admin, they now have to give cluster-wide access to acm-vm-extended:view, which would allow access to all pods, nodes, persistentvolumes, pod logs, and a lot more. This seems to go against the main purpose of fine grained rbac, which is the ability to assign the least amount of privileges for a VM admin.
Version-Release number of selected component (if applicable): 2.16.0-232
How reproducible: always
Steps to Reproduce:
- Assign fine grained rbac permissions shown in 1st rbac UI screen shot
- View fleet virtualization tree view
Actual results:
Tree view does not display.
Expected results:
Tree view should display with minimal kubevirt.io permissions, and not require read access to all cluster namespaces.