Details
-
Bug
-
Resolution: Obsolete
-
Major
-
None
-
quay-v3.6.0
-
False
-
False
-
0
Description
Description:
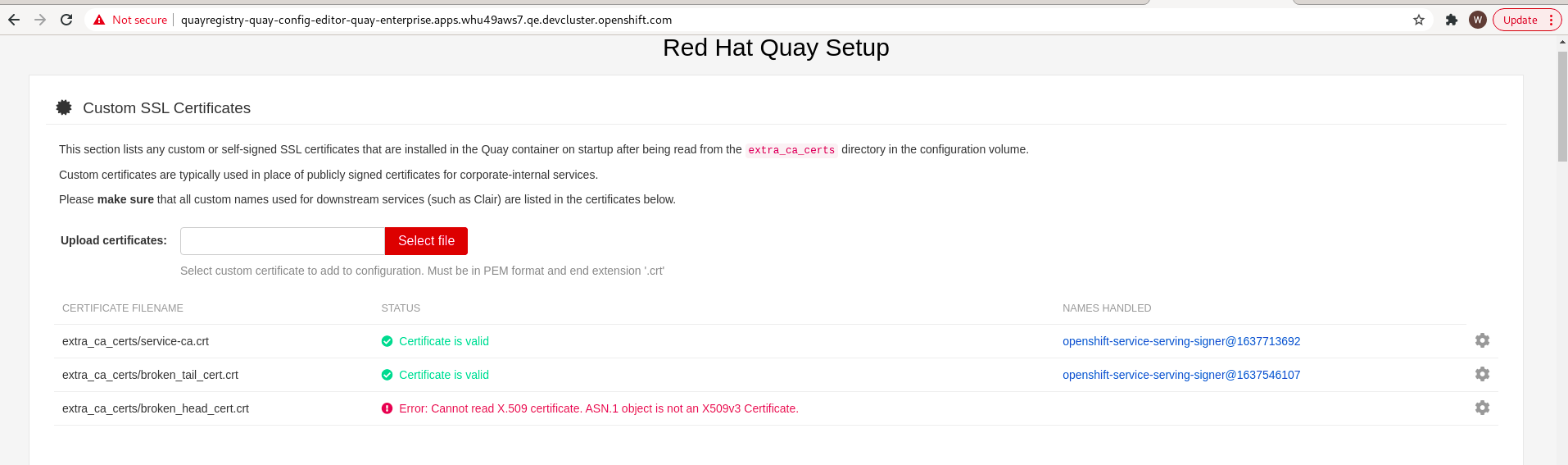
When upload broken structure certificates by config editor web console, found if the certificate which was broken in head, config editor can distinguish the error, but if the certificate which was broken in tail, config editor can not.
Version-Release number of selected component (if applicable):
$ oc get $(oc get pod -l name=quay-operator-alm-owned -o name -n quay-enterprise) -o jsonpath='
{.spec.containers[0].image}' -n quay-enterprise
registry.redhat.io/quay/quay-operator-rhel8@sha256:ed4bd0462c25674816db58242bf4631663a22731db58f958b69bd34937e01255
How reproducible:
always
Steps to Reproduce:
1. prepared two valid certificates, delete the second line from one, delete the last but one line from another
2. open config eidtor web console and upload these two broken certificates
3. check the certificate status
Actual results:
the certificate broken in head got "Error: Cannot read X.509 certificate. ASN.1 object is not an X509v3 Certificate."
but the certificate broken in tail got "Certificate is valid"
Expected results:
The certificate broken in tail should get "Error: Cannot read X.509 certificate. ASN.1 object is not an X509v3 Certificate." too.
Additional info
Prepared a valid certificate such like below
$ cat valid.crt -----BEGIN CERTIFICATE----- MIIDUTCCAjmgAwIBAgIIHU/5diucTNIwDQYJKoZIhvcNAQELBQAwNjE0MDIGA1UE Awwrb3BlbnNoaWZ0LXNlcnZpY2Utc2VydmluZy1zaWduZXJAMTYzNzU0NjEwNzAe ........ dILPPHlBQQnEdzJej4Etmwu8EeYejNWSnZRVpxXZfCSo2GyPOraHnRCbNL7xKqsd +CqRvFKfH2I/eKtYnOCegM3Z4BR2+WvmTLshLx5vsIvs7ujwjw== -----END CERTIFICATE-----
$ cp valid.crt broken_head_cert.crt $ cp valid.crt broken_tail_cert.crt
Delete one line in broken_head_cert.crt and broken_tail_cert.crt
$ cat broken_head_cert.crt -----BEGIN CERTIFICATE----- Awwrb3BlbnNoaWZ0LXNlcnZpY2Utc2VydmluZy1zaWduZXJAMTYzNzU0NjEwNzAe ........ dILPPHlBQQnEdzJej4Etmwu8EeYejNWSnZRVpxXZfCSo2GyPOraHnRCbNL7xKqsd +CqRvFKfH2I/eKtYnOCegM3Z4BR2+WvmTLshLx5vsIvs7ujwjw== -----END CERTIFICATE-----
$cat broken_tail_cert.crt -----BEGIN CERTIFICATE----- MIIDUTCCAjmgAwIBAgIIHU/5diucTNIwDQYJKoZIhvcNAQELBQAwNjE0MDIGA1UE Awwrb3BlbnNoaWZ0LXNlcnZpY2Utc2VydmluZy1zaWduZXJAMTYzNzU0NjEwNzAe ........ dILPPHlBQQnEdzJej4Etmwu8EeYejNWSnZRVpxXZfCSo2GyPOraHnRCbNL7xKqsd -----END CERTIFICATE-----
$ openssl x509 -in broken_head_cert.crt -noout -text unable to load certificate 140642057930560:error:0D0680A8:asn1 encoding routines:asn1_check_tlen:wrong tag:crypto/asn1/tasn_dec.c:1130: 140642057930560:error:0D07803A:asn1 encoding routines:asn1_item_embed_d2i:nested asn1 error:crypto/asn1/tasn_dec.c:290:Type=X509 140642057930560:error:0906700D:PEM routines:PEM_ASN1_read_bio:ASN1 lib:crypto/pem/pem_oth.c:33:
$ openssl x509 -in broken_tail_cert.crt -noout -text
unable to load certificate
140408648865600:error:0D07209B:asn1 encoding routines:ASN1_get_object:too long:crypto/asn1/asn1_lib.c:91:
140408648865600:error:0D068066:asn1 encoding routines:asn1_check_tlen:bad object header:crypto/asn1/tasn_dec.c:1118:
140408648865600:error:0D07803A:asn1 encoding routines:asn1_item_embed_d2i:nested asn1 error:crypto/asn1/tasn_dec.c:290:Type=X509
140408648865600:error:0906700D:PEM routines:PEM_ASN1_read_bio:ASN1 lib:crypto/pem/pem_oth.c:33:
